Most IoT projects fail. Not because the device doesn't work. Because the platform wasn't built for what comes after launch.
Afero has spent more than ten years building a friction-free platform to onboard customers and millions of devices, survive a cyberattack, and meet demanding scale overnight.

Secure Foundation
If it's a connected device, it's also a potential target for cyber attack. This is why we help architect security and privacy from the foundation.
End-to-End Security
Guarantee device security from supply chain to customer, device to cloud, cloud to mobile app, user to device.
Trusted Devices
Each device is uniquely credentialed with a hardware root of trust and provisioned through the supply chain before it ever reaches a customer's hands.
Secure Connections
Afero allows devices to communicate securely through any available channel for better security, resilience, and ultimately a superior customer experience.
Secure the Data
All data flows through multiple "tunnels" of protection, encrypting data in transit and authenticating all data paths.
Secure Onboarding
Afero's onboarding is fast for customers and airtight for your brand with no tradeoff between user experience and security.

Market Speed
Rolling out a robust IoT solution does not have to take months or years. Our integrated IoT solution features everything you need to create a successful line of IoT products, giving you maximum control with minimum effort.
Rapid Dev
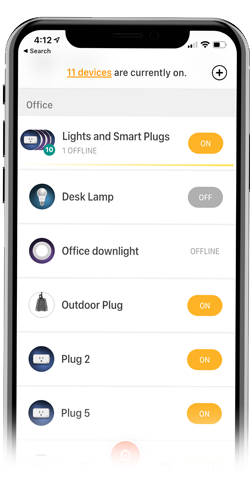
Afero gives you a low-code drag-and-drop development environment that is already aware that there is an embedded device, that mobile apps are required, and that cloud back-ends need to be in sync.
Flawless Onboarding
Through Afero's simple, secure onboarding process, you can expect to experience everything from higher customer retention rates to fewer customer support issues.
Responsive Devices
Devices respond in milliseconds, not seconds. Afero's architecture eliminates the latency and dropped-command frustration that drives product returns and one-star reviews.
Customer Success
We've designed our app to be as simple as possible, allowing customers to enjoy their smart products without worrying about the setup process or dealing with failures. Automatic failover from Afero saves time, saves aggravation, and sometimes saves the day.
Reuse at Scale
Build on the Afero platform and reuse up to 90% of your work from product to product. Transform recurring infrastructure costs into a one-time strategic decision.

Proven at Scale
Afero powers Hubspace, one of North America's largest smart home ecosystems, with millions of devices, 50+ manufacturer partners, 200+ product categories, and a 4.8-star app rating sustained across all of it.
Build-it-alone trap
Only Afero has the knowledge and ten-plus years of experience to get IoT right. Afero customers skip the DIY tax.
Total Solution
IoT is not one thing or even a few things. It's layers of proven expertise, across a broad spectrum, all built into the Afero Platform.
Spend Wisely
By leveraging the Afero Platform's tools, such as Afero edge, cloud, developer tools, and core/cross platform services, you can build and provision more profitably.
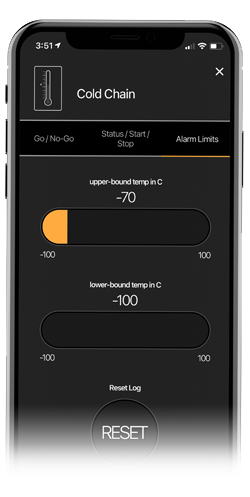
Data Trove
Monitor and manage your IoT deployment in a single dashboard, speeding up your time-to-market and making sure you have everything you need once you get there.
Last-Mile Brilliance
Afero's patented onboarding process uses a combination of security and communication technologies to create a simple and seamless experience that enables customers to connect easily and, more importantly, fully understand the usefulness of their IoT product.